We Took Control of the Fake Job Platform From the Inside
HACKADEMY'S HACKS
W.Ighodaro
4/24/20263 min read
A report came in about a platform that had been posing as a remote job recruitment service.
People were applying, uploading documents, and even paying processing fees. Everything about the platform was carefully designed to look legitimate. The dashboards were clean, the application process looked structured, and the responses felt professional.
However, one pattern was consistent.
Nobody ever got the job.
That alone was enough to confirm that this was not a normal platform. This was a controlled system built to exploit trust.
We approached the situation as a live operation.
The objective was not just to observe the system. The objective was to gain access, understand how it worked, and expose the weaknesses being used to target people.
We started by mapping out the backend of the application.

The result immediately revealed that the system had several sensitive endpoints exposed. The presence of administrative and backup routes without any form of restriction indicated that the application was not properly secured.
We moved directly to the administrative panel.
There was no login prompt. There was no authentication process. The panel loaded immediately, which confirmed a complete failure in access control.
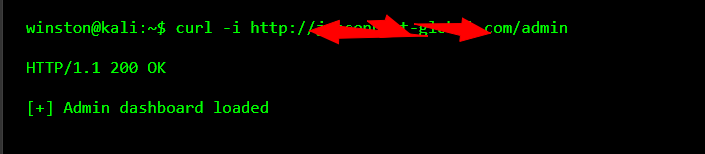
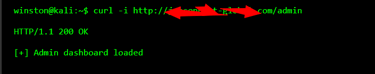
At this point, access had been established.
Once inside the panel, the structure of the operation became very clear. The system contained records of user applications, payment statuses, uploaded documents, and internal logs. This was not a basic scam page. It was a fully structured backend designed to manage victims at scale.
However, access to the panel alone was not enough.
We needed to understand how the system handled data internally.
We shifted our focus to the API.
Applications like this depend heavily on APIs to manage data flow between the frontend and backend. If the API is weak, it becomes the easiest point of exploitation.
We tested the API with a direct request.
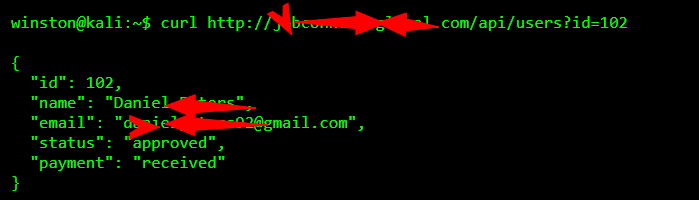
The response confirmed a second critical vulnerability.
The API allowed direct access to user records using a simple parameter. There was no validation in place to ensure that the request was authorized. This meant that any user record could be accessed by simply changing the identifier.
We did not stop there.
We continued enumerating multiple records by adjusting the ID parameter, and every request returned valid data. This exposed the entire user database.
At this stage, we had full visibility into the system.
However, we wanted to confirm whether the platform was storing backups.
The presence of a backup endpoint earlier suggested that sensitive data might be stored without protection.
We tested it directly.
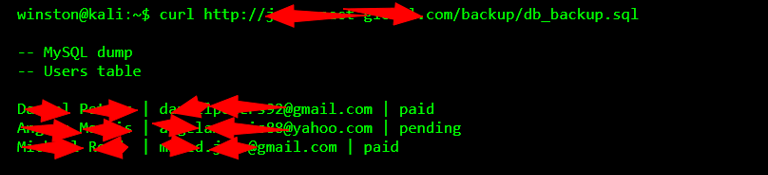
This confirmed the final piece.
The system had no real security controls in place. Sensitive user data was fully exposed, and the entire operation relied on the assumption that nobody would look deeper.
At this point, control had been established.
We had access to the administrative system, visibility into user data, and confirmation of how the platform was operating.
The system was not hacked through force.
It was accessed because it was left open.
