How We Uncovered Suspicious Data Exfiltration from a Compromised Workstation
HACKADEMY'S HACKS
5/1/20263 min read


We were brought into this case after a company’s IT team noticed something unusual about one of their employee machines. The system was not slow, there were no pop-ups, and antivirus did not flag anything. But network usage on that workstation was consistently higher than normal, even during off-hours. That was enough to raise suspicion.
This was not an ethical hacking engagement. This was a digital forensics investigation. Our job was to determine whether data was leaving the system and, if so, how it was happening.
We started by collecting network traffic from the affected machine. At this point, we were not assuming malware. We were simply observing behavior.
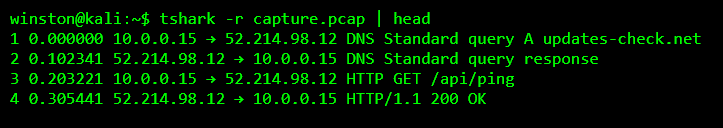
At first glance, the traffic looked normal. DNS queries, HTTP requests, nothing out of place. But experience has taught us that suspicious activity rarely looks obvious. It blends in with legitimate traffic.
So instead of looking at everything, we narrowed our focus. We filtered for DNS activity specifically, because DNS is often abused for stealthy communication.
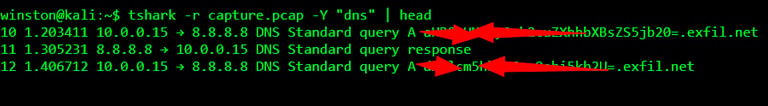
This is where things started to get serious. The DNS queries were not normal domain names. They contained what looked like encoded data. That long string before .exfil.net was not random. It had structure.
We paused here and analyzed the pattern. The strings looked like Base64 encoding. That usually means data is being packaged and sent in a readable format.
To confirm, we extracted one of the strings and decoded it.
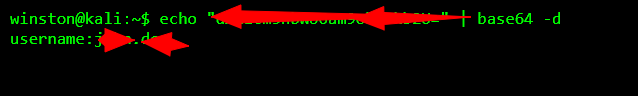
At that moment, everything became clear. The system was not just making DNS requests. It was sending data inside those requests. That is a classic DNS exfiltration technique.
But we needed more proof. We continued extracting and decoding multiple entries to understand what kind of data was being leaked.
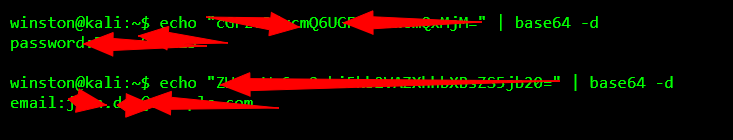
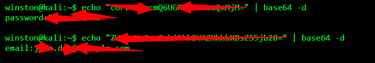
Now we had confirmation. Sensitive information, including usernames, passwords, and email addresses, was being encoded and sent out through DNS queries to an external domain. This was not normal traffic. This was data exfiltration.
We shifted into analysis mode. The next question was how this was happening. DNS exfiltration does not happen on its own. Something on that machine was generating those requests.
We reviewed the system processes and startup entries provided by the IT team. Eventually, we identified a suspicious background script running under a legitimate-looking name. It was quietly collecting data and sending it out in small chunks to avoid detection.
The outcome of this investigation was critical. The affected machine was isolated immediately. The malicious process was removed, and all compromised credentials were reset. The company also blocked outbound DNS requests to unknown domains and implemented stricter monitoring.
The lesson here is very important. Not all attacks are loud. Some of the most dangerous ones are completely silent. No alerts, no warnings, just data slowly leaving your system.
Another key takeaway is that DNS, which most people trust blindly, can be used as a covert channel for exfiltration. That is why monitoring and analyzing DNS traffic is not optional. It is essential.
In conclusion, this case shows that real-world investigations are not about guessing. They are about observing patterns, asking the right questions, and following the evidence step by step. That is how we uncover what others miss.
